I got an e-mail asking for my bank details.
From: Michael Doyle <ventas@farbiq.com.ar>
To: undisclosed recipients:;
Reply to: logistica.industrialparts@gmail.com
Subject: Re: URGENT PROFORMA INVOICE
Hello Dear, Greetings
Our company has approved the attached purchase order. Please review the purchase order list, and return to us proforma invoice with your receiving bank account for payment.
I wait for your reply.
Thanks
Michael L. Doyle
President
Direct: +1 978.834.0505 x12
Email: md@ppsystems.com
with an attached file PURCHASE QUOTATION LIST sxlx..zip , a compressed “zip” archive file that suggests it’s a Microsoft Office Excel spreadsheet. This is a scam! Bad writing, it’s not specifically addressed to me, the three e-mail addresses don’t match, I’ve never heard of the company, and there’s no reason to compress a real Office.xlsx (or .docx, etc.) file, which is already compressed. If you get something like this, mark it as junk/spam, and if it claims to be from a legit company do a web search for “company name report phishing e-mail” and forward it to the e-mail address any good company should provide.
Excel? XL SX? sxlx?
But for fun let’s investigate what’s going on. First, save the attachment to a temporary folder. The part of the filename before the extension in PURCHASE QUOTATION LIST sxlx..zip implies it contains an Excel spreadsheet (the Excel file extension is .xlsx), but in reality it is meaningless; the zip file could contain any set of files with any names. I’m on Linux, so start a terminal and type some commands to examine the zip file. (There might be Windows or Mac equivalents to these commands; on Windows you can install the Windows Subsystem for Linux for maximum geekery.) To start let’s test and list (using -tv options) its contents.
% unzip -tv /tmp/PURCHASE\ QUOTATION\ LIST\ sxlx..zip
Archive: /tmp/PURCHASE QUOTATION LIST sxlx..zip
PURCHASE QUOTATION LISTs͏x͏l͏x͏..exe: mismatching "local" filename (PURCHASE QUOTATION LISTтАоs═Пx═Пl═Пx═П..exe),
continuing with "central" filename version
testing: PURCHASE QUOTATION LISTs͏x͏l͏x͏..exe OK
At least one warning-error was detected in /tmp/PURCHASE QUOTATION LIST sxlx..zip.Notice there’s a reversed message from the unzip program here. The name of the one file in the zip archive very likely has some special character codes in it that changes text display into right-to-left mode (for languages such as Hebrew), and they spill over into the display of the message, making it hard to read and importantly, obscuring the order of the letters in the file’s name. If you copy and paste only the word “gnihctamsim” above and paste it somewhere else the letters appear the right way round, because you probably didn’t copy the character code that flips the order of the visible letters; and if you click at the start of the message and drag to the right to select it you’ll see the selection highlight jump around as the selection feedback tries to show you selecting the end of the text and then less and less of the backwards text. (The details of how this blog post appears depend on how your browser handles special characters – download Firefox!) The warning message is mismatching “local” filename :exe..xlxs , warning that the file extension doesn’t match what it appears to be, and I think that triggers the final “At least one warning-error was detected…” message. In Windows, a file with a .exe extension can be an executable file, a binary program of computer instructions that can literally do anything: show a fun game, forward your sensitive documents to a foreign computer, encrypt all your files and demand a ransom, install malware that will forever mine Bitcoins or spy on you, and worse! Here the exe part seems to come before the ending ..xlxs and it’s the “final” dot-whatever that influences how the operating system treats the file. But because the text has gone into right-to-left mode, it looks like blab blah exe blah.xlxs, which almost looks like the file extension for a spreadsheet so maybe people will ignore the warning, assuming it even shows up on Windows built-in zip file handling. (I don’t know what the point of the weird characters TтАоs═Пx═Пl═Пx═П in the file are before/after the right-to-left “TSIL”/LIST.)
Let’s actually use the unzip utility to uncompress the zip file it into a temporary subfolder. This would be risky on Windows, but I’m on Linux and I don’t think I have any Windows emulators or WINE (“Wine Is Not an Emulator”) that can actually run the file, and I’ll be careful not to accidentally run or “double-click” it.
% mkdir /tmp/PURCHASE_QUOTATION_quarantine
% cd /tmp/PURCHASE_QUOTATION_quarantine
% unzip ../PURCHASE\ QUOTATION\ LIST\ sxlx..zip
Archive: ../PURCHASE QUOTATION LIST sxlx..zip
PURCHASE QUOTATION LISTs͏x͏l͏x͏..exe: mismatching "local" filename (PURCHASE QUOTATION LISTтАоs═Пx═Пl═Пx═П..exe),
continuing with "central" filename version
inflating: PURCHASE QUOTATION LISTs͏x͏l͏x͏..exe That looks OK, because it looks like it ends in “.xlsx”. But with all the right-to-left and mirror writing crap going on, does it really?
What’s really at the end? What is the end in the middle?
Let’s try to get a listing of the one file we uncompressed:
% ls --size
appears to my eyes as 2396 'PURCHASE QUOTATIONLISTsxlx..exe'
pastes here as 2396 'PURCHASE QUOTATION LISTs͏x͏l͏x͏..exe'
% type *.exe[Tab]
expands to % PURCHASE\ QUOTATION\ LIST<202e>s<034f>x<034f>l<034f>x<034f>..exeHere’s where it gets extra weird. The one file in the archive uncompressed into a 2,396 kilobyte (2 Megabytes or so) file. What I see in the terminal is ‘PURCHASE QUOTATION LISTsxlx..exe, which is BAD, it’s an executable. But when I copy-pasted it into the paragraph above, it appears backwards with .xlxs on the end. It’s only when I expand the filename on the command line by pressing [Tab] or when I view the directory contents in my editor (vim) that I see the escape codes messing this up. And I’m now in a mess of what’s actually in the file name versus the terminal escape codes that tell the terminal to display things in bold and go into reverse mode and such. I wasted time trying to find a set of arguments to utilities hexdump, od, and strings that would print the regular letters and reveal the Unicode code points (or terminal escape characters?), e.g.
% ls *.exe | strings --unicode=x
PURCHASE QUOTATION LIST<0xe280ae>s<0xcd8f>x<0xcd8f>l<0xcd8f>x<0xcd8f>..exeI even asked ChatGPT to write a program to get the filename in the directory and print it out using Unicode escapes for the code points. After some coaxing it politely and helpfully wrote a 30-line Python program that when run prints:
% python3 ~/bin/dirlist_codepoints.py
Original: PURCHASE QUOTATION LISTs͏x͏l͏x͏..exe
Code Points: PURCHASE QUOTATION\u0020LIST\u00e2\u0080\u00aes\u00cd\u008fx\u00cd\u008fl\u00cd\u008fx\u00cd\u008f..exeHow come none of these agree? Is it really that complicated? (Yes, it is.)
Careful with that tfeL-ot-thgiR
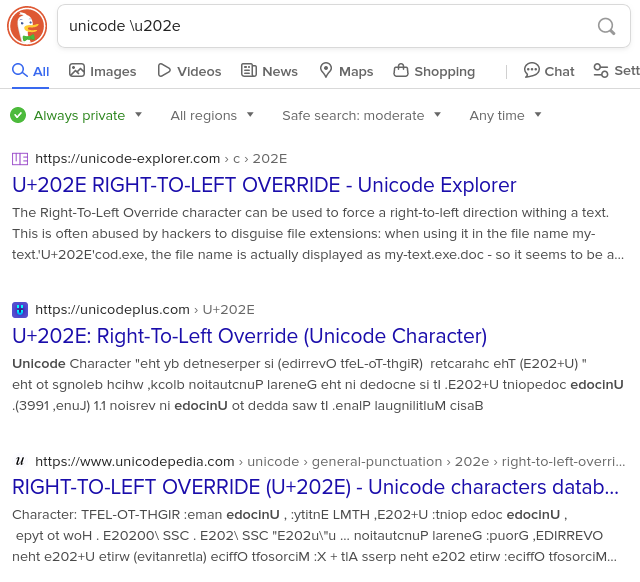
What is the 202e when the file name first starts to display weird? Most sequences of text these days use Unicode to represent regular “typewriter” characters, accented characters, symbols, hieroglyphs, Asian logographs, emoji, and the thousands of other “characters” we now put in text. A DuckDuckGo web search for “unicode \202e” reveals
U+202E RIGHT-TO-LEFT OVERRIDE – Unicode Explorer
The Right-To-Left Override character can be used to force a right-to-left direction withing a text. This is often abused by hackers to disguise file extensions: when using it in the file name my-text.’U+202E’cod.exe, the file name is actually displayed as my-text.exe.doc – so it seems to be a.docfile while in reality it is an.exefile. There’s even an xkcd comic for this character!
So that’s the explanation for the start of the problem and why part of the filename and text nearby appear reversed. I’ll leave the decoding of the rest of the weird characters to actual security and Unicode professionals.
Danger nerd humor alert
What’s extreme nerd humor is many of the search results are from useless web sites that try to appear high in search results with computer-generated web pages for every possible Unicode character, like “Unicode Character ![]() (U+1F48C) is ‘LOVE LETTER’…” (together with a bunch of ads and privacy-sucking JavaScript tracking). But when the page “shows” the Right-to-Left Override “character,” the snippet in search results (and the web site’s page, but don’t go there) appears in reverse.
(U+1F48C) is ‘LOVE LETTER’…” (together with a bunch of ads and privacy-sucking JavaScript tracking). But when the page “shows” the Right-to-Left Override “character,” the snippet in search results (and the web site’s page, but don’t go there) appears in reverse.
![]() ha. ha. ha.
ha. ha. ha. ![]()
What is the executable?
Let’s not run it!, even under Linux.Instead use the file utility to see what kind of file it is.
% file PURCHASE\ QUOTATION\ LIST<202e>s<034f>x<034f>l<034f>x<034f>..exe
PURCHASE QUOTATION LISTs͏x͏l͏x͏..exe: PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sectionsAny utility that displays the file’s name without extreme care is going to have reversed output, and file does too. The right-to-left text is telling us it’s an assembly, for MS Windows, 2 sections sxlx..exe: PE32+ executable (GUI) x86-64 Mono/.Net. You can write a 2 MB standalone program that does a hell of a lot of bad stuff, but who knows what the executable section would do. I wonder if there’s actually a spreadsheet in there as well as computer code. For fun let’s see what strings of characters are in it.
% strings *.exe | less
!This program cannot be run in DOS mode.
.text
...
oT8=
<?xml version="1.0" encoding="UTF-8" standalone="yes"?>
<assembly xmlns="urn:schemas-microsoft-com:asm.v1" manifestVersion="1.0">
<assemblyIdentity version="1.0.0.0" name="MyApplication.app"/>
<trustInfo xmlns="urn:schemas-microsoft-com:asm.v2">
<security>
<requestedPrivileges xmlns="urn:schemas-microsoft-com:asm.v3">
<requestedExecutionLevel level="asInvoker" uiAccess="false"/>
</requestedPrivileges>
</security>
</trustInfo>
</assembly>
xkcva2wfKaiDsaDdws,
...
%xkcva2wfKaiDsaDdwsPAPADDINGXXPAPADDINGXXPAPADDINGXX...PADDINGXX repeated thousands of times sover and over and over...PADDINGXXPAPADDIN
(END)So there is some kind of program in there announcing that it wants to run with my privileges, which when I boot into Windows is an administrator with lots of rights.
scary stuff!
